CompTIA Network+ Demo Questions
Here you can find CompTIA Network+ exam sample questions which will help you to prepare for your upcoming certification test. These questions will give you an idea of what to expect on the exam and help you review the N10-008 study material. Be sure to go over the Free N10-008 questions multiple times so that you are confident and comfortable with the material. You can always go to the full N10-008 dumps here.
These CompTIA Network+ certification questions are designed to give you a feel for the material you'll be tested on. They cover a wide range of topics, so you can get a sense of what to expect on examination day.
These N10-008 dumps are updated regularly, so you can be confident that you're studying with the most up-to-date information available. We also provide answer keys so that students can check their work.
Additionally, going through CompTIA Network+ practice questions can help you identify any areas where you need more review. Taking advantage of our N10-008 demo questions is a great way to set yourself up for success on the real thing.
These CompTIA Network+ questions cover the material that will be on the test, and provide an opportunity for students to practice their skills. The questions are designed to be similar to those that will be on the actual CompTIA Network+ exam, so that students can get a feel for what they will be facing. We believe that by providing these demo questions, students will be better prepared and more likely to succeed on their exams.
Good luck for the N10-008 exam!
CompTIA Network+ Sample Questions:
1. Two remote offices need to be connected securely over an untrustworthy MAN. Each office needs to access network shares at the other site. Which of the following will BEST provide this functionality?
A. Client-to-site VPN
B. Third-party VPN service
C. Site-to-site VPN
D. Split-tunnel VPN
2. A network technician needs to correlate security events to analyze a suspected intrusion Which of the following should the technician use?
A. SNMP
B. Log review
C. Vulnerability scanning
D. SIEM
3. During the security audit of a financial firm the Chief Executive Officer (CEO) questions why there are three employees who perform very distinct functions on the server. There is an administrator for creating users another for assigning the users lo groups and a third who is the only administrator to perform file rights assignment Which of the following mitigation techniques is being applied'
A. Privileged user accounts
B. Role separation
C. Container administration
D. Job rotation
4. Which of the following systems would MOST likely be found in a screened subnet?
A. RADIUS
B. FTP
C. SQL
D. LDAP
5. A company that uses VoIP telephones is experiencing intermittent issues with one-way audio and dropped conversations The manufacturer says the system will work if ping times are less than 50ms. The company has recorded the following ping times:
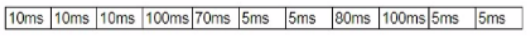
Which of the following is MOST likely causing the issue?
A. Attenuation
B. Latency
C. VLAN mismatch
D. Jitter
6. A network device is configured to send critical events to a syslog server; however, the following alerts are not being received: Severity 5 LINK-UPDOWN: Interface 1/1, changed state to down Severity 5 LINK-UPDOWN: Interface 1/3, changed state to down Which of the following describes the reason why the events are not being received?
A. The network device is not configured to log that level to the syslog server
B. The network device was down and could not send the event
C. The syslog server is not compatible with the network device
D. The syslog server did not have the correct MIB loaded to receive the message
7. A technician is writing documentation regarding a company’s server farm. The technician needs to confirm the server name for all Linux servers. Which of the following commands should the technician run?
A. ipconfig
B. nslookup
C. arp
D. route
8. Which of the following is MOST commonly used to address CVEs on network equipment and/or operating systems?
A. Vulnerability assessment
B. Factory reset
C. Firmware update
D. Screened subnet
9. A firewall administrator is implementing a rule that directs HTTP traffic to an internal server listening on a non-standard socket Which of the following types of rules is the administrator implementing?
A. NAT
B. PAT
C. STP
D. SNAT
E. ARP
10. Which of the following BEST describes a network appliance that warns of unapproved devices that are accessing the network?
A. Firewall
B. AP
C. Proxy server
D. IDS