CompTIA Security+ Demo Questions
Here you can find CompTIA Security+ exam sample questions which will help you to prepare for your upcoming certification test. These questions will give you an idea of what to expect on the exam and help you review the SY0-701 study material. Be sure to go over the Free SY0-701 questions multiple times so that you are confident and comfortable with the material. You can always go to the full SY0-701 dumps here.
These CompTIA Security+ certification questions are designed to give you a feel for the material you'll be tested on. They cover a wide range of topics, so you can get a sense of what to expect on examination day.
These SY0-701 dumps are updated regularly, so you can be confident that you're studying with the most up-to-date information available. We also provide answer keys so that students can check their work.
Additionally, going through CompTIA Security+ practice questions can help you identify any areas where you need more review. Taking advantage of our SY0-701 demo questions is a great way to set yourself up for success on the real thing.
These CompTIA Security+ questions cover the material that will be on the test, and provide an opportunity for students to practice their skills. The questions are designed to be similar to those that will be on the actual CompTIA Security+ exam, so that students can get a feel for what they will be facing. We believe that by providing these demo questions, students will be better prepared and more likely to succeed on their exams.
Good luck for the SY0-701 exam!
CompTIA Security+ Sample Questions:
1. A tax organization is working on a solution to validate the online submission of documents The solution should be earned on a portable USB device that should be inserted on any computer that is transmitting a transaction securely. Which of the following is the BEST certificate for these requirements?
A. User certificate
B. Self-signed certificate
C. Computer certificate
D. Root certificate
2. Which of the following BEST reduces the security risks introduced when running systems that have expired vendor support and lack an immediate replacement?
A. Implement proper network access restrictions
B. Initiate a bug bounty program
C. Classify the system as shadow IT.
D. Increase the frequency of vulnerability scans
3. Which of the following organizations sets frameworks and controls for optimal security configuration on systems?
A. ISO
B. GDPR
C. PCI DSS
D. NIST
4. An organization wants to implement a biometric system with the highest likelihood that an unauthorized user will be denied access. Which of the following should the organization use to compare biometric solutions?
A. FRR
B. Difficulty of use
C. Cost
D. FAR
E. CER
5. An engineer recently deployed a group of 100 web servers in a cloud environment. Per the security policy, all web-server ports except 443 should be disabled. Which of the following can be used to accomplish this task?
A. Application allow list
B. SWG
C. Host-based firewall
D. VPN
6. A social media company based in North Amenca is looking to expand into new global markets and needs to maintain compliance with international standards With which of the following is the company's data protection officer MOST likely concerned''
A. NIST Framework
B. ISO 27001
C. GDPR
D. PCI-DSS
7. A company suspects that some corporate accounts were compromised. The number of suspicious logins from locations not recognized by the users is increasing Employees who travel need their accounts protected without the nsk of blocking legitimate login requests that may be made over new sign-in properties. Which of the following security controls can be implemented?
A. Enforce MFA when an account request reaches a nsk threshold
B. Implement geofencing to only allow access from headquarters
C. Enforce time-based login requests that align with business hours
D. Shift the access control scheme to a discretionary access control
8. During a recent incident an external attacker was able to exploit an SMB vulnerability over the internet. Which of the following action items should a security analyst perform FIRST to prevent this from occurring again?
A. Check for any recent SMB CVEs
B. Install AV on the affected server
C. Block unneeded TCP 445 connections
D. Deploy a NIDS in the affected subnet
9. Several users have opened tickets with the help desk. The help desk has reassigned the tickets to a secunty analyst for further review The security analyst reviews the following metrics:
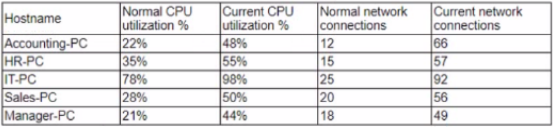
Which of the following is MOST likely the result of the security analyst's review?
A. The ISP is dropping outbound connections
B. The user of the Sales-PC fell for a phishing attack
C. Corporate PCs have been turned into a botnet
D. An on-path attack is taking place between PCs and the router
10. A security analyst is investigating suspicious traffic on the web server located at IP address 10.10.1.1. A search of the WAF logs reveals the following output:
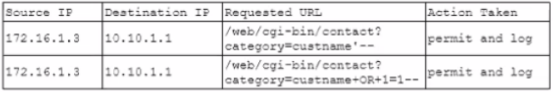
Which of the following is MOST likely occurring?
A. XSS attack
B. SOLi attack
C. Replay attack
D. XSRF attack