Implementing and Operating Cisco Security Core Technologies Demo Questions
Here you can find Implementing and Operating Cisco Security Core Technologies exam sample questions which will help you to prepare for your upcoming certification test. These questions will give you an idea of what to expect on the exam and help you review the 350-701 SCOR study material. Be sure to go over the Free 350-701 SCOR questions multiple times so that you are confident and comfortable with the material. You can always go to the full 350-701 SCOR dumps here.
These Implementing and Operating Cisco Security Core Technologies certification questions are designed to give you a feel for the material you'll be tested on. They cover a wide range of topics, so you can get a sense of what to expect on examination day.
These 350-701 SCOR dumps are updated regularly, so you can be confident that you're studying with the most up-to-date information available. We also provide answer keys so that students can check their work.
Additionally, going through Implementing and Operating Cisco Security Core Technologies practice questions can help you identify any areas where you need more review. Taking advantage of our 350-701 SCOR demo questions is a great way to set yourself up for success on the real thing.
These Implementing and Operating Cisco Security Core Technologies questions cover the material that will be on the test, and provide an opportunity for students to practice their skills. The questions are designed to be similar to those that will be on the actual Implementing and Operating Cisco Security Core Technologies exam, so that students can get a feel for what they will be facing. We believe that by providing these demo questions, students will be better prepared and more likely to succeed on their exams.
Good luck for the 350-701 SCOR exam!
Implementing and Operating Cisco Security Core Technologies Sample Questions:
1. When Cisco and other industry organizations publish and inform users of known security findings and vulnerabilities, which name is used?
A. Common Security Exploits
B. Common Vulnerabilities and Exposures
C. Common Exploits and Vulnerabilities
D. Common Vulnerabilities, Exploits and Threats
2. Which network monitoring solution uses streams and pushes operational data to provide a near real-time view of activity?
A. SNMP
B. SMTP
C. syslog
D. model-driven telemetry
3. What Cisco command shows you the status of an 802.1X connection on interface gi0/1?
A. show authorization status
B. show authen sess int gi0/1
C. show connection status gi0/1
D. show ver gi0/1
4. What are two Detection and Analytics Engines of Cognitive Threat Analytics? (Choose two)
A. data exfiltration
B. command and control communication
C. intelligent proxy
D. snort
E. URL categorization
5. A mall provides security services to customers with a shared appliance. The mall wants separation of management on the shared appliance. Which ASA deployment mode meets these needs?
A. routed mode
B. transparent mode
C. multiple context mode
D. multiple zone mode
6. What is the primary difference between an Endpoint Protection Platform and an Endpoint Detection and Response?
A. EPP focuses on prevention, and EDR focuses on advanced threats that evade perimeter defenses.
B. EDR focuses on prevention, and EPP focuses on advanced threats that evade perimeter defenses.
C. EPP focuses on network security, and EDR focuses on device security.
D. EDR focuses on network security, and EPP focuses on device security.
7. What is the function of Cisco Cloudlock for data security?
A. data loss prevention
B. controls malicious cloud apps
C. detects anomalies
D. user and entity behavior analytics
8. An engineer needs a solution for TACACS+ authentication and authorization for device administration. The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
A. Cisco Prime Infrastructure
B. Cisco Identity Services Engine
C. Cisco Stealthwatch
D. Cisco AMP for Endpoints
9. Which two probes are configured to gather attributes of connected endpoints using Cisco Identity Services Engine? (Choose two)
A. RADIUS
B. TACACS+
C. DHCP
D. sFlow
E. SMTP
10. Refer to the exhibit.
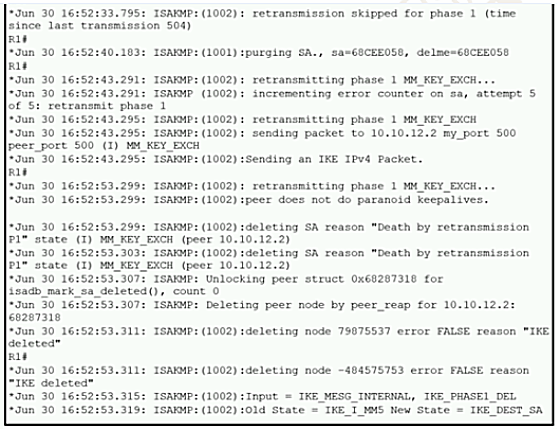
A network administrator configured a site-to-site VPN tunnel between two Cisco IOS routers, and hosts are unable to communicate between two sites of VPN. The network administrator runs the debug crypto isakmp sa command to track VPN status. What is the problem according to this command output?
A. hashing algorithm mismatch
B. encryption algorithm mismatch
C. authentication key mismatch 6
D. interesting traffic was not applied