CompTIA CySA+ Demo Questions
Here you can find CompTIA CySA+ exam sample questions which will help you to prepare for your upcoming certification test. These questions will give you an idea of what to expect on the exam and help you review the CS0-002 study material. Be sure to go over the Free CS0-002 questions multiple times so that you are confident and comfortable with the material. You can always go to the full CS0-002 dumps here.
These CompTIA CySA+ certification questions are designed to give you a feel for the material you'll be tested on. They cover a wide range of topics, so you can get a sense of what to expect on examination day.
These CS0-002 dumps are updated regularly, so you can be confident that you're studying with the most up-to-date information available. We also provide answer keys so that students can check their work.
Additionally, going through CompTIA CySA+ practice questions can help you identify any areas where you need more review. Taking advantage of our CS0-002 demo questions is a great way to set yourself up for success on the real thing.
These CompTIA CySA+ questions cover the material that will be on the test, and provide an opportunity for students to practice their skills. The questions are designed to be similar to those that will be on the actual CompTIA CySA+ exam, so that students can get a feel for what they will be facing. We believe that by providing these demo questions, students will be better prepared and more likely to succeed on their exams.
Good luck for the CS0-002 exam!
CompTIA CySA+ Sample Questions:
1. A user reports the system is behaving oddly following the installation of an approved software application. The application executable was sourced from an internal third-party repository Which of the following will ensure the application is valid?
A. Ask the user to refresh the existing definition file for the antivirus software
B. Perform a malware scan on the file in the internal repository
C. Hash the application's installation file and compare it to the hash provided by the vendor
D. Remove the user's system from the network to avoid collateral contamination
2. Which of the following BEST describes the primary role ol a risk assessment as it relates to compliance with risk-based frameworks?
A. It demonstrates the organization's mitigation of risks associated with internal threats.
B. It serves as the basis for control selection.
C. It prescribes technical control requirements.
D. It is an input to the business impact assessment.
3. A security analyst reviews SIEM logs and detects a well-known malicious executable running in a Windows machine The up-to-date antivirus cannot detect the malicious executable Which of the following is the MOST likely cause of this issue?
A. The malware is being executed with administrative privileges.
B. The antivirus does not have the mltware's signature.
C. The malware detects and prevents its own execution in a virtual environment.
D. The malware is fileless and exists only in physical memory.
4. A security analyst has discovered malware is spreading across multiple critical systems and is originating from a single workstations, which belongs to a member of the An cyber-infrastructure team who has legitimate administrator credentials. analysis of the traffic indicates the workstation swept the networking looking for vulnerable hosts to infect. Which of the following would have worked BEST to prevent the spread of this infection?
A. Vulnerability scans of the network and proper patching.
B. A properly configured and updated EDR solution.
C. A honeypot used to catalog the anomalous behavior and update the IPS.
D. Logical network segmentation and the use of jump boxes
5. A security analyst is reviewing the following log from an email security service.
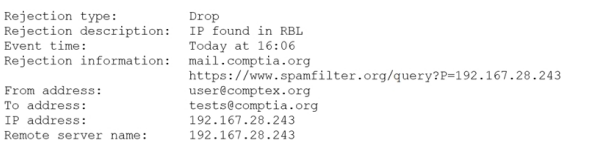
Which of the following BEST describes the reason why the email was blocked?
A. The To address is invalid.
B. The email originated from the www.spamfilter.org URL.
C. The IP address and the remote server name are the same.
D. The IP address was blacklisted.
E. The From address is invalid.
6. A security analyst recently discovered two unauthorized hosts on the campus's wireless network segment from a man-m-the-middle attack .The security analyst also verified that privileges were not escalated, and the two devices did not gain access to other network devices Which of the following would BEST mitigate and improve the security posture of the wireless network for this type of attack?
A. Enable MAC filtering on the wireless router and suggest a stronger encryption for the wireless network,
B. Change the SSID, strengthen the passcode, and implement MAC filtering on the wireless router.
C. Enable MAC filtering on the wireless router and create a whitelist that allows devices on the network
D. Conduct a wireless survey to determine if the wireless strength needs to be reduced.
7. A web-based front end for a business intelligence application uses pass-through authentication to authenticate users The application then uses a service account, to perform queries and look up data m a database A security analyst discovers employees are accessing data sets they have not been authorized to use. Which of the following will fix the cause of the issue?
A. Change the security model to force the users to access the database as themselves
B. Parameterize queries to prevent unauthorized SQL queries against the database
C. Configure database security logging using syslog or a SIEM
D. Enforce unique session IDs so users do not get a reused session ID
8. Which of the following secure coding techniques can be used to prevent cross-site request forgery attacks?
A. Input validation
B. Output encoding
C. Parameterized queries
D. Tokenization
9. A security analyst is trying to determine if a host is active on a network.
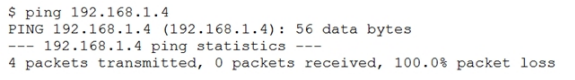
The analyst first attempts the following:
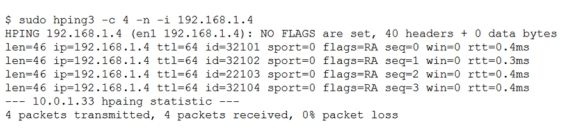
The analyst runs the following command next: Which of the following would explain the difference in results?
A. ICMP is being blocked by a firewall.
B. The routing tables for ping and hping3 were different.
C. The original ping command needed root permission to execute.
D. hping3 is returning a false positive.
10. White reviewing incident reports from the previous night, a security analyst notices the corporate websites were defaced with po mcai propaganda. Which of the following BEST Describes this type of actor?
A. Hacktivist
B. Nation-state
C. insider threat
D. Organized crime